Passwords are the most common authentication measures taken by the enterprises, yet passwords are easily hackable and notoriously insecure. The end users tend to be careless while managing the passwords. They frequently share and reuse the same passwords. This is where multi-factor authentication comes in picture.
A Brief About MFA
Multi-Factor Authentication (MFA) is an umbrella term for verifying the identity of end users with a password and at least one other way of authentication. The other way of authenticating can be either through email, phone, browser push notifications, device -based, or biometrics. MFA ensures that the user accounts stay secure even if the credentials are compromised.
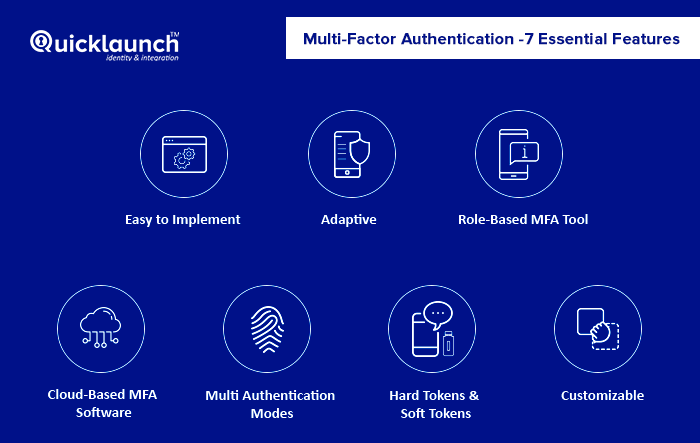
Multi-Factor Authentication – 7 Essential Features
When it comes to something as critical as Multi-Factor Authentication software, it gets a lot imperative because of the stakes involved. MFA is typically used to provide extra layer of security preventing unauthorized access. But, when there is plethora of choices in the market, you will often find yourself in a confused state. To help you out, we have listed down a list of features you need to look while selecting a MFA software.
1. Easy to Implement
One of the biggest challenges faced by IT departments of the organizations that are eager to switch to MFA is deploying it into existing identity environments, especially when that environment includes both on-premise and cloud apps. You should always look for an MFA software with flexible deployment options (on-premises or as a service) which will make deployment much easier.
2. Adaptive
The Enterprise mobility and BYOD have made it easier for the users to access sensitive information from remote locations using different devices. This poses grave challenges in terms of data security and compliance. Adaptive multi-factor authentication solves this problem by giving the users flexibility to securely access their resources from anywhere at any time. The MFA tool should sense that a user has logged in from different place using different device and put in front the challenges to identify the user identity. This will prevent the unauthorized access, just in case someone else is trying to access the user’s resources – in an event such as lost/stolen device etc.
3. Role-Based Multi-Factor Authentication Tool
You often have people with different privilege levels and roles in an organization. A one-mode-fits-all approach to user authentication is surely not the best approach in this scenario. The MFA software must trigger role-based authentication for different set of users. This will be helpful in managing the privileged accounts having access to sensitive data and reinforce security.
4. Cloud-Based Multi-Factor Authentication Software
The number of cloud applications that is used in the Enterprise or Higher-Ed Institutions is ever-increasing. Whether it is Email, CRM, ERP, Productivity apps or anything, everything is moving to the cloud. This applies to MFA as well. Cloud-based multi-factor authentication software means that you don’t have to worry about the availability and manageability. It is imperative to stay relevant to the changing times.
5. Multi Authentication Modes
Multiple authentication modes such as email, phone, browser push notifications, device based authentication, challenge questions, and Touch ID, not only give your users the flexibility but also a great way to boost overall security. Some modes that you need to look out for are:
- Email Authentication - The email with a verification link or code is sent to the user. The user needs to click on the link or enter the verification code to access the resources.
- Phone Verification - When you are trying to access your account, you will receive a one-time password (OTP) on your phone via SMS or call. The OTP should be entered to login to your account.
- Browser Push Notifications - A push notification is generated on the browser that pushes the verification code and helps in the authentication process by verifying the user identity.
- Biometrics - Based MFA is the most secure authentication method that is difficult to break. Touch ID verification, voice recognition, or retina scanning can be done to authenticate the user access.
6. Hard Tokens & Soft Tokens
A small hardware device such as key fob or smart card generates a one-time password to authenticate the user session. The users must carry the hard token along to use this means of MFA. A soft token (one-time password) is generated by an application or software for authenticating the user identity. Most of the organizations prefer using soft tokens as the hard tokens can be stolen or lost.
7. Customizable
The Enterprise IT must be able to customize the MFA software such as by empowering the end users to manage their devices and choose if MFA is required for those devices. This will deliver superior end user experience and provide them flexibility to use different devices in a secure way.
Your evaluation criteria should include the 7 above-mentioned aspects while choosing an MFA vendor, so that you can prevent unauthorized access and strengthen the end user security in your organization.