Implementing IAM in Your Organization: A Framework

According to the Global Risks Report (2022) “Cybersecurity failure” is one of the risks that worsened the most through COVID-19, with “cyber insurance pricing in the United States rising by 96% in the third quarter of 2021.”
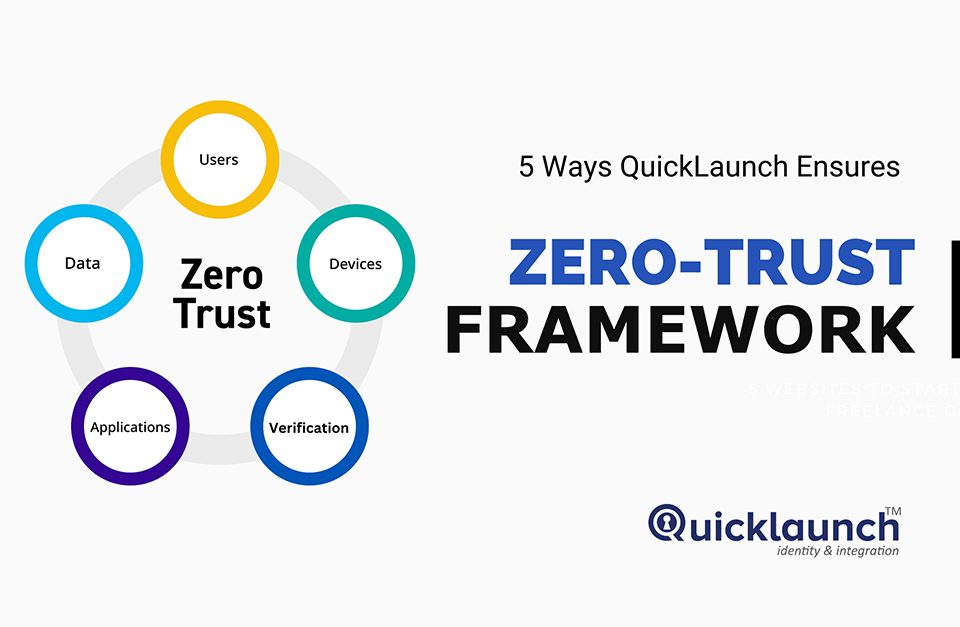
Now, in a world where cyberattacks and digital threats are constantly evolving, business executives and IT teams are constantly under pressure to prevent unwarranted access to company resources. Assigning the right privileges and establishing a Zero Trust approach for end-users has become quintessential for the safety of organizations. However, implementing and maintaining an effective IAM system requires a smart allocation of current IT resources.
This framework can help organizations get started by outlining the key steps organizations need to take to design, deploy, and adopt IAM.
Why is IAM important?
According to IBM, Identity and Access Management is “the security discipline that makes it possible for the right entities (people or things) to use the right resources (applications or data) when they need to, without interference, using the devices they want to use.”
With hybrid remote work, most organizations’ processes take place off-premises. This increases the chances of user impersonation and the exposure of critical assets. CIOs and tech executives must then provide safe access for remote users, including contractors and business partners. When properly adopted, IAM can increase business productivity and accelerate workflows while providing a safe environment for organizations.
Key Components of IAM
To understand and adopt IAM, organizations must build upon two key components:
- User Access: Services and related users, all of which are managed as a group, providing or denying access.
- Policies: Defining which groups have access to specific resources. Setting standards and role-based access depending on service and user levels.
In order to set these policies and grant user access, organizations can use the following IAM tools: Single Sign-on (SSO), Multi-Factor Authentication, Adaptive Authentication, Automated provisioning, Cloud AD, and Mobile Apps solutions.
- SSO: A Single Sign-On Solution can reduce friction for users and provide a less constraining experience. By using a one-time, single set of login credentials, users can access what they need, when they need it. SSO solutions like QuickLaunch can also help with User Provisioning and De-Provisioning. Allowing IT to quickly change users whenever their role or project changes, or when they join/leave the company.
- Password Manager with MFA: Two-factor authentication (2FA) and Multi-Factor Authentication (MFA) are the most effective against credential stuffing and suspicious login attempts. There are different types of factors:
- 1: Knowledge Factor: Something users know, such as passwords, PINs, or even secret locks.
- 2: Possession Factor: Something users carry with them, such as a key or smart card.
- 3: Inherence Factor: Something users unmistankingly are, like biometric verification (fingerprint, retina scan, or voice recognition).
- Adaptive Authentication: A risk-based authentication approach in which the system assesses login scenarios to determine which type of authentication policies to enforce. With Adaptive Authentication, there are different types of digital authentication methods such as traditional passwords, pre-shared keys (PSK), behavioral authentication, and biometrics. Biometrics is currently the most precise authentication method, with Windows Hello becoming a default security option for students and enterprise solutions. Whether through facial recognition, fingerprints, and others, biometrics are still unmatched.
- Automated Provisioning: Granting and revoking access, reassigning users, or changing their projects is draining. IT can spend countless hours working on manually provisioning users. With an Automated Provisioning solution like QuickLaunch such tasks could be automated instead.
- Cloud Directory: With Cloud Directory, organizations can rely on a cloud-based identity and access management service for employees to access external resources and other SaaS applications.
- All of these tools are interconnected to a Mobile App, so users can access safely, wherever they are.
The Real Value of IAM
Safety is the main benefit of laying out a robust IAM strategy. Allowing IT to have a broader control of user access is also a relief that allows employees to focus on their work. Besides the obvious benefits there are other perks of using IAM:
- Granting system access to business partners and other actors, in a safe environment, consolidating trust for partners.
- Complying with the Health Insurance Portability and Accountability Act (HIPA) and the Sarbanes-Oxley Act (SOX).
- Allow IT to automate security tasks by reducing password requests and handling routine tasks in smarter ways.
- Enhances productivity and drives innovation, allowing for collaboration between on-premises users and collaborators.
Getting Access
An examination of existing and legacy systems is the best way to start building an IAM solution. Identifying gaps and opportunities early and often, and interacting with stakeholders. True to the two key components of IAM, the idea is to create a list of all user groups and access situations, as well as a basic set of requirements, and challenges before implementing IAM.
Experience QuickLaunch in action. Schedule a Demo and speak to our IAM experts to set your first line of defense against cyberthreats.