Eliminate Passwords.
Strengthen Security. Simplify Access.
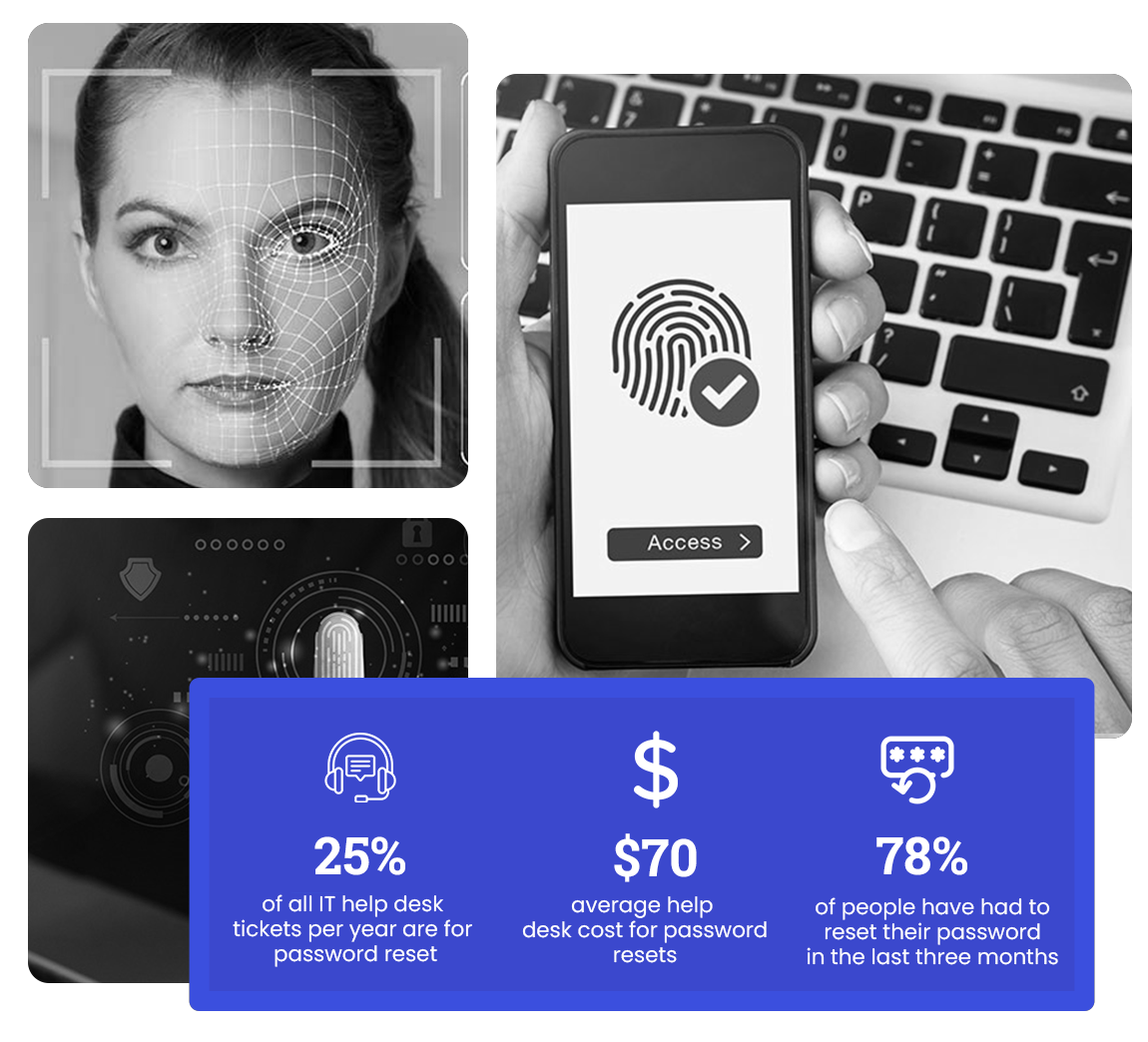
Passwords remain the leading cause of data breaches. QuickLaunch Passwordless replaces outdated credentials with phishing-resistant authentication methods that are both secure and user-friendly. Whether using Face ID, a security key or push notification, users can log in seamlessly – without the risk of reused or compromised credentials.
QuickLaunch Passwordless empowers users to access applications using biometrics, mobile push or security keys — no passwords required.
Passwordless Features
One step closer to a passwordless future.

Push Notifications
Authenticate instantly by approving a real-time push notification sent to the user’s mobile device via the QuickLaunch app.
Authenticators
Add an extra layer of security using trusted apps like DUO, Google Authenticator or Microsoft Authenticator.
Email Verification
A one-time verification code is sent to the user’s registered email address, for secure, password-free login.

SMS One-Time Passcode (OTP)
Users receive a OTP via SMS to verify their identity quickly and securely.
Security Questions
Use predefined questions as an additional identity verification step when needed.

Preferred Authentication
Let users select their preferred authentication method for a personalized login experience.
YubiKey
Leverage FIDO2-compliant hardware keys like YubiKey to deliver strong, phishing-resistant authentication with enterprise-grade security.
Empowering institutions through strategic partnerships